Query Domain Controller User Login Sessions

Not only user account name is fetched but also users ou path and computer accounts are retrieved.
Query domain controller user login sessions. In my test environment it took about 4 seconds per computer on average. To query other sessions the user must have special access permission. Note that this could take some time. It s a long story.
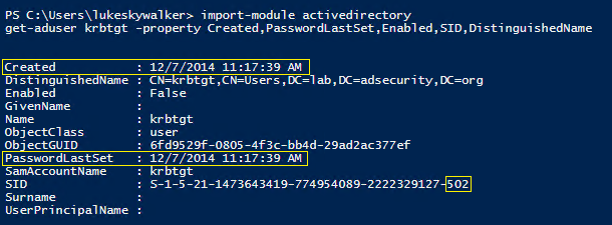
This script will list the ad users logon information with their logged on computers by inspecting the kerberos tgt request events eventid 4768 from domain controllers. The session end time can be obtained using the event id 4647 is 11 24 2017 at 03 02 pm. Let s use an example to get a better understanding. I have it available on pro and enterprise skus of win10 and my brother confirmed that query user and quser are not available on win10 1909 home.
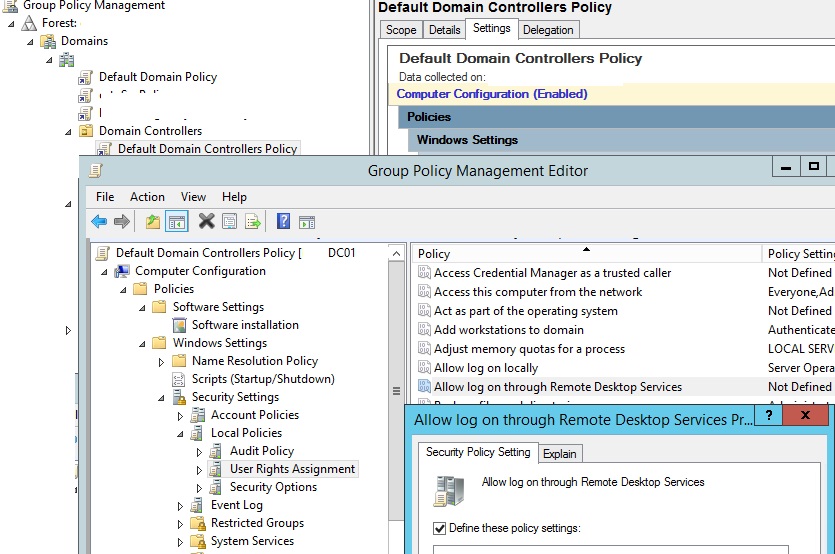
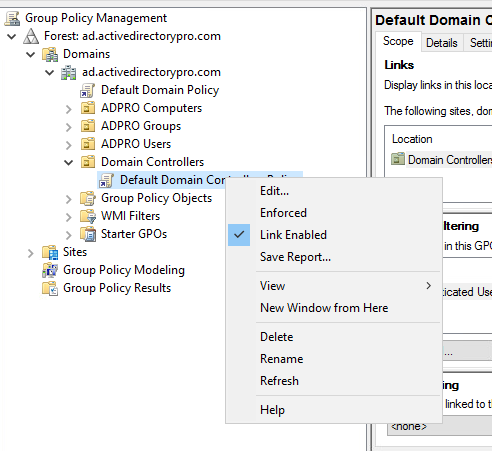
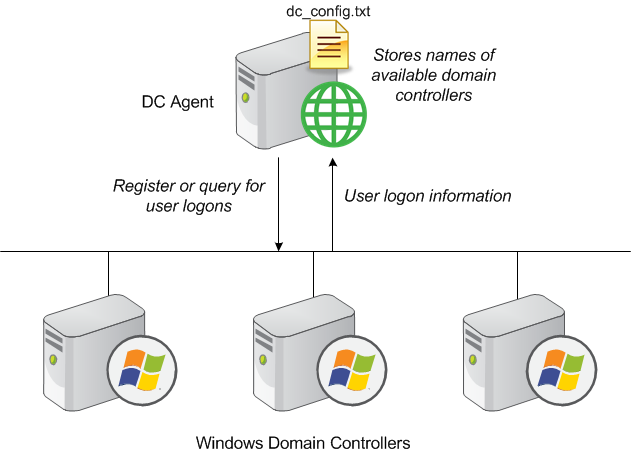
The target is a function that shows all logged on users by computer name or ou. For example if a user logs on anywhere on the network using a domain account their authentication request is sent to a domain controller. It is better to create a new security group in the domain for example allowlogondc and add user accounts to it that need remote access to the dc. It s a question i was asked to try and accomplish fellas.
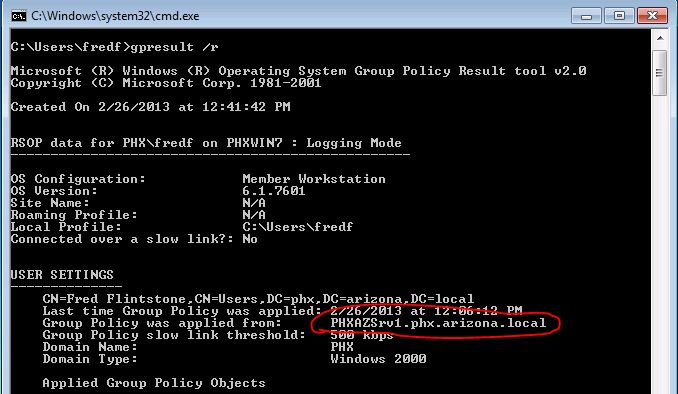
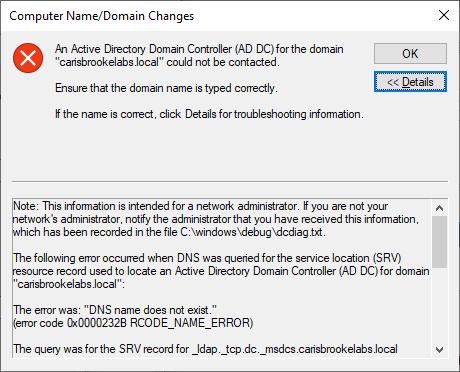
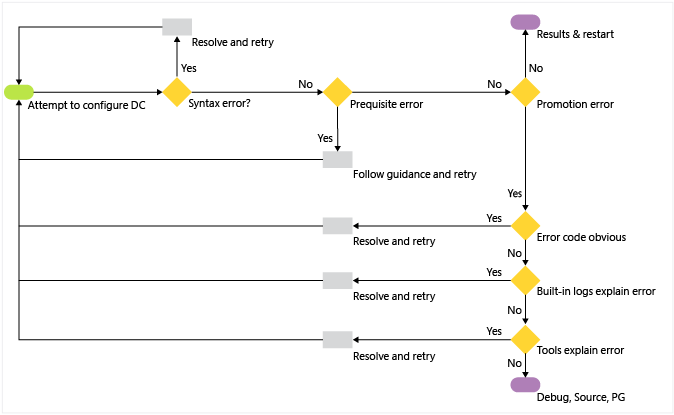
The request is sent to the first dc from the list of domain controllers and events related to the selected user are queried and saved into a variable. A user can always query the session to which the user is currently logged on. When the domain controller fails the authentication request the local workstation will log 4625 in its local security log noting the user s domain logon name and the failure reason. Query event logs for selected user.
There is a different failure reason for every reason a windows logon can failure in contrast with the more general result codes generated by the kerberos. I want to know if they are authenticating to the local dc or going out to the cloud dc s. She logged in at. Since you cannot rdp into a home sku it s a bit irrelevant to run this command locally.
In the following steps the list of events is saved and the process of extracting valuable information from the gathered events will be started. User logon event properties. If you don t specify a session using the username sessionname or sessionid parameters this query will display information about all active sessions in the system. The reasoning wouldn t really help the question.
It s also possible to query all computers in the entire domain. Failed kerberos authentication attempts will appear as event id 4771 at the domain controller. Getting the logged on user of client01.
.jpeg)